How a Google API Key Became an $8,000 AI Bill, Meta Scam Ads Lawsuit, and 73-Second Cyber Attacks
Google Cloud customers are reporting shocking surprise bills after compromised or misused API keys were allegedly used to access expensive Gemini AI services. In one case, Rod Dinan says his monthly Google Cloud costs jumped from under $50 to nearly $8,000. Sydney developer Isuru Fonseka says he was hit despite setting spending controls, raising broader […]
Meta Staff Revolt Over AI, Anthropic Caps Agents, Google’s AI Laptop Surprise
Meta employees are pushing back against workplace monitoring software reportedly tracking mouse and keyboard activity, raising fresh questions about morale, trust, and whether internal culture could derail the company’s AI ambitions. Anthropic has partially reversed restrictions that frustrated Claude users relying on third-party AI agent tools, but there’s a catch: new monthly usage credit pools […]
Tech Layoffs Surge Again, Lake Tahoe Power Crisis, Amazon AI Gaming, and ‘Unionizing’ AI
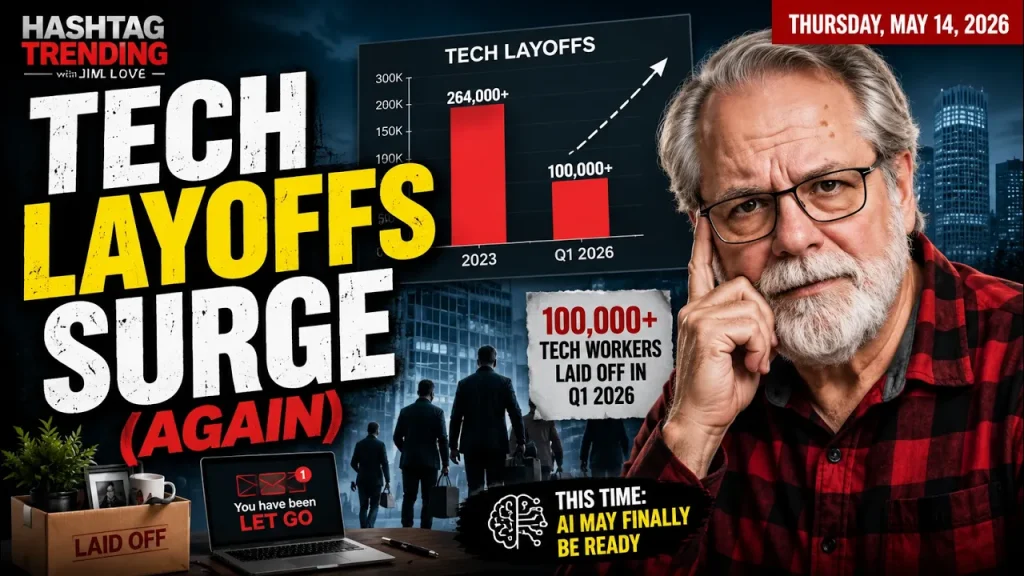
Tech layoffs are accelerating again, and the numbers are starting to look uncomfortably familiar. In this May 14, 2026 episode of Hashtag Trending, host Jim Love covers five major tech stories shaping business, AI, infrastructure, and the future of work. More than 100,000 tech workers have already been laid off in 2026, putting the year […]
Canvas Breach ‘Deal’ With ShinyHunters, AI Zero-Day Warning, Checkmarx Hit Again
Cybersecurity Today examines a troubling set of new security developments affecting schools, software supply chains, and account security. Instructure says it reached an “agreement” with the ShinyHunters threat group after the massive Canvas breach that may have affected up to 275 million users across 9,000 educational institutions. Reports indicate attackers exploited multiple cross-site scripting (XSS) […]
OpenAI’s New Enterprise AI Play, Reddit Blocks Mobile Users, WhatsApp Encryption Fight Goes On

OpenAI is making a major move into enterprise services with The Deployment Company, sending its own engineers into customer organisations to help companies finally turn AI pilots into real business systems. Is this the start of direct competition with consulting giants like Accenture, Deloitte, IBM Consulting, and even partner Capgemini? Also in this episode: Reddit […]
Claude Can Dream? AI Data Center Backlash, GM Privacy Fallout & Canvas Breach
Anthropic says Claude is getting dramatically more capable — effectively unlimited context, multi-agent coordination, interactive self-correction, and even an experimental background learning process it calls “dreaming.” At the same time, Anthropic admits Claude Code is growing far faster than expected, raising a bigger question: can the company control what it is creating? In today’s Hashtag […]
Canvas Breach Exposes 275M Accounts | AI Targets Water Systems | GM OnStar Settlement
A massive cybersecurity week. On this episode of Cybersecurity Today, David Shipley breaks down the reported breach of Instructure’s Canvas learning platform, where attacks linked to the ShinyHunters extortion group may have exposed data tied to up to 275 million user accounts across more than 9,000 educational institutions. The incident disrupted access, delayed exams, and […]
Meta allegedly made billions from scam advertising while online fraud explodes worldwide.

In this special edition of Cybersecurity Today, David Shipley speaks with scam-fighting expert Erin West about the global fraud crisis, the rise of AI-powered scams, and why traditional law enforcement may be falling behind. Cybersecurity Today would like to thank Material Security for supporting this podcast. Material security provides. faster, more complete detection and response […]
AI Gadgets Get Worse, US-China AI Talks, Taiwan Train Hack | Hashtag Trending

Is artificial intelligence starting to make consumer technology worse instead of better? In today’s Hashtag Trending with Jim Love: The United States and China may be opening talks on artificial intelligence safety, military risks, and AI guardrails — even as the technology race between the two countries accelerates. At the same time, a new trend […]
AI Goes Offshore: Thiel’s Ocean Data Centres, Shopify Cuts, Google AI Backlash

Peter Thiel is backing a radical new idea—floating AI data centres powered by ocean waves. It sounds like science fiction, but serious investors are on board, and it could change how the world powers artificial intelligence. In today’s episode of Hashtag Trending, we break down four major tech stories shaping the industry: Why Thiel and […]